In a striking demonstration of modern digital vulnerability, Derek Muller of Veritasium collaborated with tech reviewer MKBHD to showcase a method for stealing $10,000 from a locked iPhone. This security flaw, initially discovered by researchers at the University of Surrey and the University of Birmingham, bypasses the layers of biometric security we have come to rely on. The experiment began by successfully charging a locked iPhone $5, eventually escalating to a $10,000 transaction, all without the owner ever touching the phone or entering a passcode.
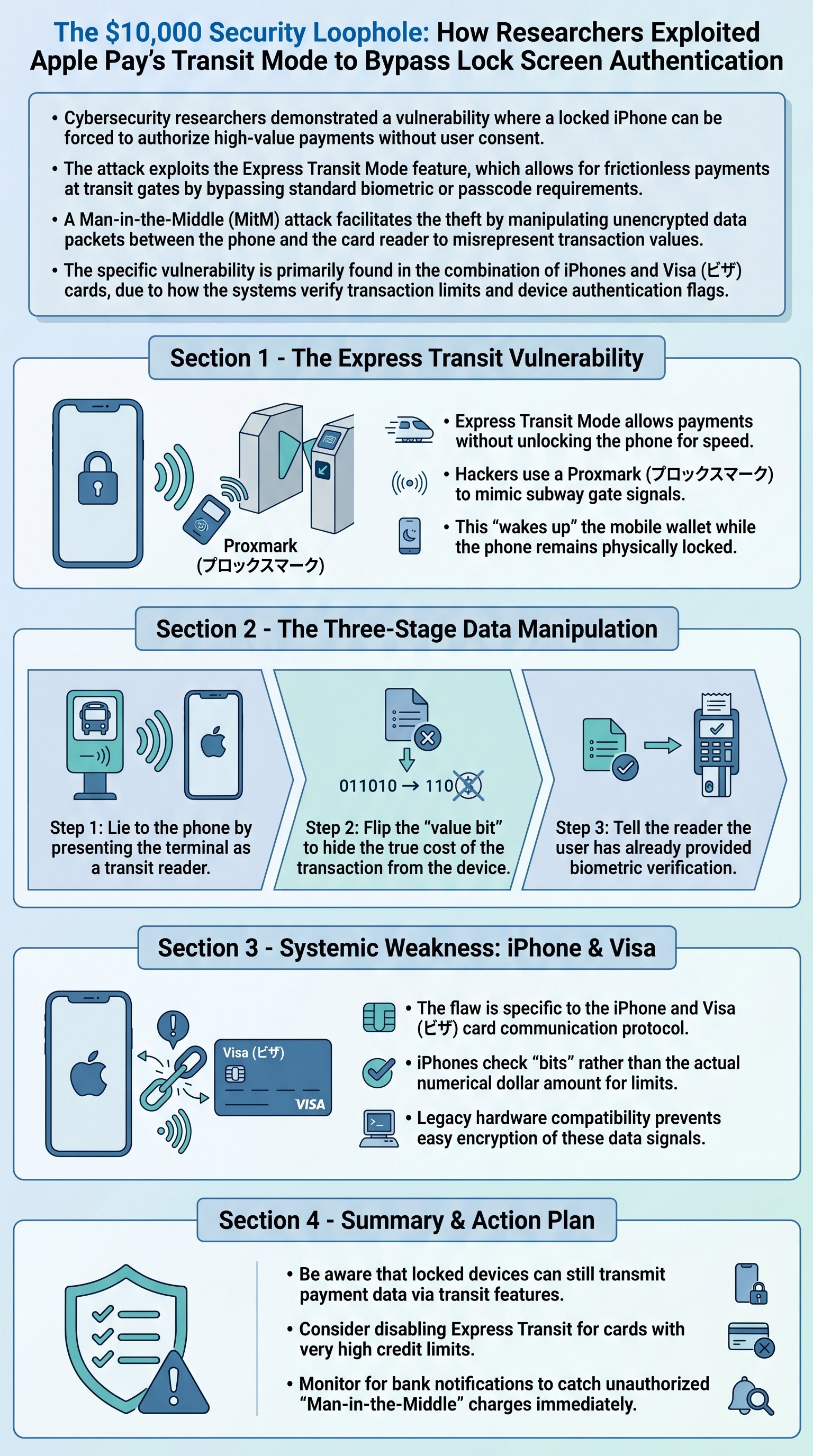
The core of the exploit lies in a feature called Express Transit Mode, introduced to allow commuters to pass through transit gates quickly without needing to unlock their phones. Professors Ioana Boureanu and Tom Chothia explained that when a phone is in this mode, it is programmed to respond automatically to signals from what it believes are transit readers. The hackers used a specialized NFC device called a Proxmark to broadcast a signal that mimics a subway gate, tricking the phone into 'waking up' its payment card for a transaction.
To bridge the gap between a simple transit fare and a massive $10,000 theft, the team utilized a 'Man-in-the-Middle' architecture. This involves a sequence of hardware: the victim's phone communicates with the Proxmark, which sends data to a laptop; the laptop then relays modified data to a burner phone, which finally interacts with a standard retail card reader. By inserting themselves into the communication flow, the researchers could intercept and alter the data packets traveling through the air in real-time.

The execution of the hack follows three specific logical 'lies' told to the hardware. Step 1: The laptop modifies the reader's request to include a specific binary code found in transit gates. This convinces the iPhone that it is interacting with a legitimate subway terminal, allowing it to bypass the lock screen. At this stage, the phone is ready to pay but expects a small, low-value amount typical of a commute.
Step 2 involves tricking the phone's internal logic regarding transaction limits. On an iPhone, the device determines whether a payment is 'high-value' or 'low-value' not by looking at the actual dollar amount, but by checking a single status bit sent by the reader. By flipping this bit from '1' (high-value) to '0' (low-value) via the Python script on the laptop, the researchers forced the iPhone to treat a $10,000 request as a negligible transit fee that requires no further user verification.
Step 3 addresses the card reader's verification requirements. While the phone now believes the transaction is low-value, the reader knows it is asking for $10,000 and expects proof of user authentication. To solve this, the researchers intercepted the phone’s response and flipped another bit to signal that 'Consumer Device Cardholder Verification' (CDCV) had been performed. This final lie satisfies the reader and the bank, resulting in a 'Green Approved' status and a printed receipt for $10,000.

The researchers noted that this specific combination of flaws is unique to the iPhone and Visa ecosystem. Unlike Android devices from manufacturers like Samsung, which often verify the actual numerical value of a transaction before authorizing an Express Transit payment, the iPhone's reliance on the reader's status bit creates a critical blind spot. Furthermore, the communication between the phone and the reader is largely unencrypted to maintain compatibility with thousands of legacy terminals worldwide, making bit manipulation possible.
While the sophisticated equipment and technical knowledge required make this attack unlikely for the average street criminal, the existence of such a loophole for over five years raises serious questions about the speed of security updates in the financial sector. For users, the primary defense is to remain vigilant and potentially disable Express Transit Mode for high-limit credit cards. This case serves as a potent reminder that convenience often comes at the cost of security, and the protocols governing our digital wallets are only as strong as their weakest unencrypted link.