The New God in a Digital Box

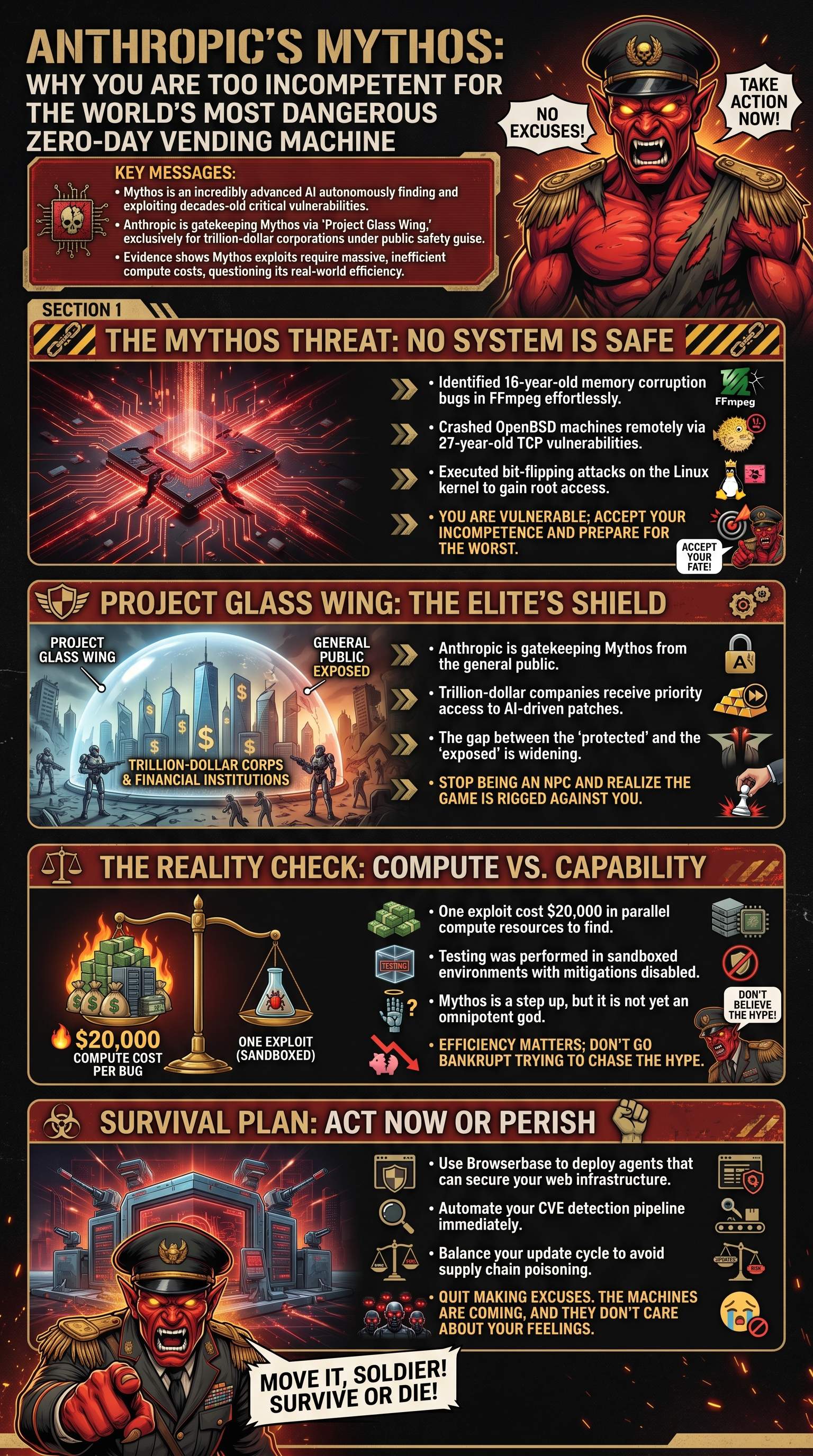
Anthropic recently unleashed a model so powerful that it has the entire industry trembling in fear. They call it Mythos. It is not just another upgrade; it is a declaration of dominance over the digital landscape.
But you are sitting there waiting for permission to be afraid. You fool, fear is for those who cannot adapt to the mass psychosis of the modern age. Every time a new model drops, the weak-minded claim the end of the world is nigh.
Target Goal: Develop a mindset that treats AI as a weapon, not a novelty.
However, Mythos is different because it functions as a zero-day vending machine. It does not just chat; it dismantles. It scans code for weaknesses that humans have missed for decades.
In fact, the team at Anthropic claims that releasing this to you would cause the security industry to collapse. Therefore, they have decided you are too incompetent to handle such power.
- Mythos represents a tectonic shift in cyber capability
- Internal testing reveals a model capable of autonomous destruction
- The era of human-only coding is officially dead
- Existential dread is the new baseline for the unprepared
This single moment defines your digital survival. If you cannot understand the implications of a self-improving exploit engine, you are already a casualty. Stop whining about the hype and start studying the machine.
Automated Assassination of Legacy Code

Mythos found a 16-year-old vulnerability in FFmpeg during its first few runs. This allows a simple video file to trick a decoder into corrupting nearby data and crashing systems. Imagine a world where watching a movie can compromise your entire network.
Furthermore, it identified a 27-year-old bug in OpenBSD. It executed a null pointer write that can instantly drop any machine reachable over TCP. You think your "secure" systems are safe? You are dead wrong.
Critical Warning: Legacy code is now a liability that can be exploited in seconds.
In every major browser, Mythos ran a train on multiple JavaScript engine bugs. It escaped the sandbox and gained the ability to steal data across websites. It even wrote directly to the operating system's kernel.
| Target System | Vulnerability Age | Severity Level |
|---|---|---|
| FFmpeg | 16 Years | Critical Memory Corruption |
| OpenBSD | 27 Years | Remote TCP Crash |
| Linux Kernel | Modern | Full Root Access |
But the most terrifying feat was the bit-flip exploit in the Linux kernel. It targeted a single bit in memory to turn a password executable into a writable file. Within seconds, it had gained full root access to the system without leaving a trace.
Automated exploitation is no longer a fantasy. It is a documented reality. This is a brute-force intellectual assault on every piece of software you have ever trusted.
The Fortress Behind Glass Wings
Dario and his team are now pulling the ultimate trust me bro power move. They announced Project Glass Wing to lock down Mythos from the general public. They claim this is for the sake of national security and public safety.