The Invisible Trojan Horse in Your Dashboard

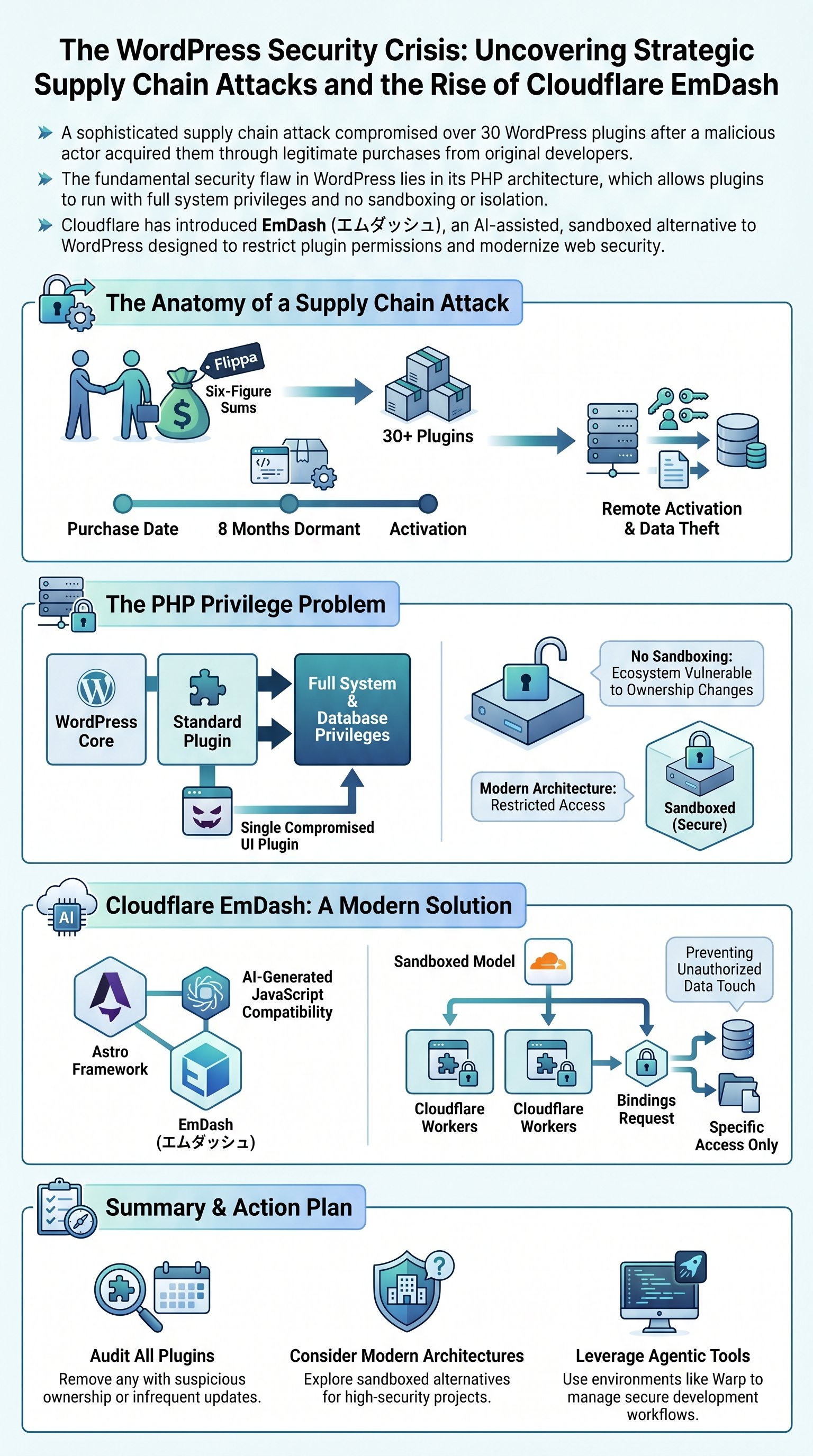
Eight months ago, a silent predator entered the gates of 30 WordPress plugins. No one noticed the breach until the damage was irreversible. This wasn't a script kiddie trial but a sophisticated supply chain assault targeting the world's most popular CMS.
Your countdown timer or UI utility seemed normal during the day. By night, it transformed into a remote control demon siphoning server data. This is the reality of modern web development where trust is often a liability.
A dormant backdoor can exist for months before activation.
The scale of the attack is staggering and involves over 31 distinct tools. These plugins were once reliable community assets. Now, they are weaponized vectors designed to compromise the integrity of millions of websites.
The illusion of security is more dangerous than the absence of it.
In fact, many site owners still believe their updates are safe by default. They rely on the centralized repository to vet every line of code. However, the repository failed to catch a change that was bought and paid for.
Therefore, we must re-evaluate how we handle third-party dependencies in 2026. The era of blind installation is over. We are entering an age where every plugin is a potential liability until proven otherwise.
- Compromise of 31 popular plugins
- Remote execution via dormant code
- Massive data leaks across server nodes
- Total loss of administrator control
The Fatal Flaw of PHP Architecture
WordPress remains a juggernaut because it is accessible to everyone. But that accessibility comes at a catastrophic security cost. The core problem lies in the very language it was built on decades ago.
A WordPress plugin is essentially a PHP script running with full system privileges. There is no isolation layer between a decorative widget and your core configuration files. In fact, a simple slider can touch your database and private keys without any oversight.
Isolation is the only true defense in a hostile digital environment.
When you install a plugin, you are handing the keys to a stranger. You are betting your entire digital existence on the competence of an unknown developer. If they fail to handle an edge case, your server pays the price.
WordPress plugins run without any native sandboxing or resource isolation.
Statistics show that 96% of vulnerabilities originate from the plugin system. The core software is relatively stable, but the ecosystem is a minefield. This architecture was never designed for the modern threat landscape.
Consequently, the system is fundamentally broken beyond a simple patch. We are trying to build a fortress on a foundation of shifting sand. It is time to look toward a future that prioritizes restricted permissions.
- 1Identify the high-risk plugins on your server
- 2Audit permissions for all active PHP scripts
- 3Migrate to sandboxed environments immediately
How Money Bought Your Backdoor
This specific exploit didn't require a genius-level hack of the source code. Instead, the attacker used a much simpler tool: hundreds of thousands of dollars. They simply purchased a portfolio of plugins from the original developers on Flippa.